Quick Guide to Static ISP Proxies
2024-01-17
Static ISP proxies are the fastest and most reliable proxy type. Companies can use them for market research, brand protection, market research, and to protect intellectual property. They are also commonly used by cybersecurity professionals. In this article we will show you how to quickly use a static ISP with PIA proxy.
1. The concept of static ISP
A static ISP refers to an Internet Service Provider (ISP) that provides a fixed IP address. Generally speaking, only special users or computers using dedicated Internet access have fixed IP addresses, and they need to pay relatively expensive fees. This static IP address is usually assigned to users, allowing users to connect directly to the Internet without the need for secondary allocation through dynamic IP addresses. In the context of literature and web application services, the word "static" means a role or attribute that remains unchanged, and a fixed IP address provided by a static ISP can be thought of as a computer's permanent address in the network.
2. Advantages of static ISP proxy in PIA proxy
a. Unlimited traffic and concurrency
b.IP validity period is 365 days+
c.Support SOCKS5/HTTP(S)
d.Support various fingerprint browsers
e.Wide coverage
f. Has stability
g. Security:
h. Efficient connection
3. Application scenarios of static ISP proxy
a. Server hosting
A static IP makes it easier for administrators and users to connect to the server. Because a static IP is constant, the server's address does not change between connections, making it easier to manage the server and maintain the application.
b. remote access
In remote access, static IP can make it more convenient for administrators to access corporate internal networks and devices. For example, if a company has multiple office locations, administrators can use static IPs to connect to servers and computers in remote offices to manage and maintain remote devices.
c. Web camera
In network surveillance systems, static IP can be used for network cameras. Static IP can ensure that the network camera always uses the same IP address, making the network monitoring system more stable and reliable.
d. Mail Server
In an enterprise's internal mail system, static IP can ensure that the mail server always uses the same IP address, thereby better protecting the security and reliability of the mail system.
e. Online game
In online games, static IPs can make it easier for players to connect to the game server. Static IP addresses make game servers easier to manage, thus improving game stability and reliability.
f. Breakthrough of website access restrictions
Many video websites and online entertainment websites restrict content access based on regions. Using static proxy IP, you can select IP addresses from different countries and regions to restrict access across regions.
g. Protect personal privacy and information security
By using a proxy IP address to protect your real IP, you can avoid leaving traces of your visits online and reduce the risk of being discovered by hackers and trackers. When conducting online consumption, banking and sensitive privacy access, using high-anonymity proxy IP can effectively protect user information security.
h. Big data collection and crawler capture
When using crawler technology for data collection, a large number of requests will be identified by the website as DDoS attacks or malicious access, and access restrictions will be imposed. The use of proxy IP pools can effectively protect the real access source, circumvent these restrictions, and complete the data collection task.
i. Simulated test environment
Some websites will have differentiated display effects or provide different website versions in different regions. At this time, static proxy IPs can be used to simulate the local network environment by selecting proxy IPs in different countries and regions for website testing and other purposes.
Network debugging and analysis:
By setting up a static proxy in the local network environment, and then routing network traffic to the proxy server through a springboard, network access data can be monitored and analyzed to find network security vulnerabilities or debug network equipment.
4. Use of static ISP
1. After you purchase the static ISP in the PIA proxy, download the client and display the proxy you purchased on the client.
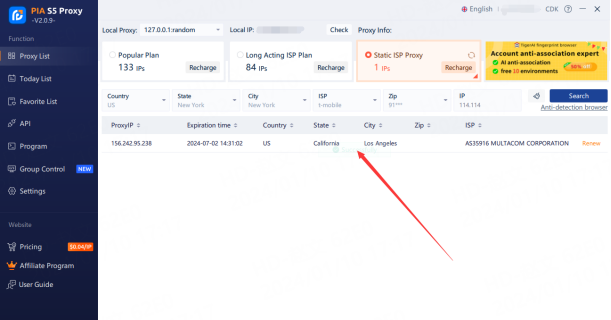
2. Extract IP and port directly on the client
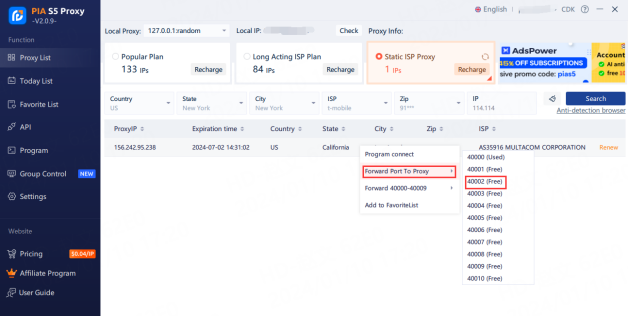
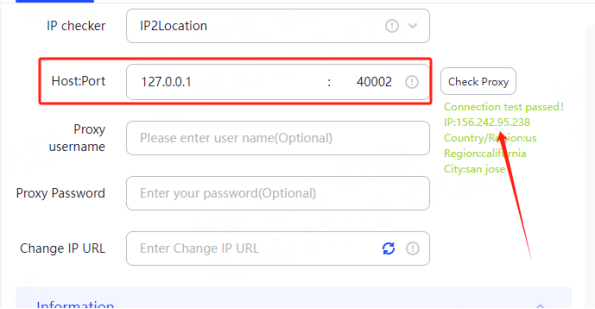
3. Configure in the browser you are using
5. Summary
If you are looking for a fast and reliable proxy, pias5proxy static ISP proxy is an excellent solution. They can be easily assembled and used with third-party software.










